Firewall System Design Service
WHAT IS FIREWALL DESIGN?
Firewalls are the primary line of defense that protects the internal network of an organization from cyber attackers and Internet threats and restricts unauthorized access. But simply installing a firewall won’t solve the problem. Even if the vendor’s offer seems promising, you have to understand how to efficiently integrate the firewall into your existing systems.
This infrastructure is mission-critical, which is why designing a firewall system implies making crucial decisions about an organization’s system security and the ways to enforce it. This includes:
- determining the problems to solve
- outlining the architecture
- choosing firewall features
- considering using dual firewalls
- selecting a firewall vendor
- establishing the system and security requirements
- defining the rules and policies defending the private network
WHY IS HAVING GOOD FIREWALL SYSTEM DESIGN IMPORTANT?
Having an effective, simple-to-manage, and scalable firewall system design is integral for businesses for several reasons:
WHICH PROBLEM DOES FIREWALL DESIGN ADDRESS?
A high-quality firewall system design answers many vital questions like:
- Which risks do you want to avoid using the firewall?
- What’s the firewall location within your systems, and which segments will it protect?
- Which services are required?
- What is the expected performance?
- Who will manage the firewall system?
- How are the system and network expected to grow?
It’s like a blueprint outlining all the network security essentials. So, if an organization has trouble making such tough decisions, turning to professionals for a consultation on firewall system design can save a lot of trouble down the line.
WHEN DO YOU WORK ON FIREWALL SYSTEM DESIGN?
Although firewall system design can be taken care of at any point, ideally, this is a step that takes place before you even purchase a firewall (i.e., prior to or during firewall sizing). In fact, the requirements indicated in the design directly affect vendor selection and the functions the firewall must have.
A lot of things depend on the firewall’s location within the system and what it’s supposed to protect. For example, this regards how much network traffic it’ll process, its size, and the must-include firewall functions.
Such decisions are often impossible to make correctly without in-depth experience. Hence, turning to firewall professionals like OutsourceIT.PRO’s team that offers a firewall system design service can be a safety net.
Have questions about the design service of firewall systems?
OUR FIREWALL SYSTEM DESIGN SERVICE STEPS
How does the firewall system design process work? Here are the common steps that OutsourceIT.PRO follows when designing a firewall system. We fall back on the best practices recommended by CERT.
Step 1: Detailed analysisFirewall system design starts with the analysis of the current environment. During this step, we review the needs and tasks the firewall should accomplish, noting the core security requirements. This will influence most consequent decisions like the appropriate firewall size you need, which vendor is optimal, how the firewall should protect the network, how to configure the firewall, and so on.
Step 2: Deciding on the basic architectureWe continue by choosing the basic components of firewall architecture. Usually, this starts with single-layer vs. multi-layer architecture, how many hosts there will be, how they’ll be connected, and the tasks they’ll perform.
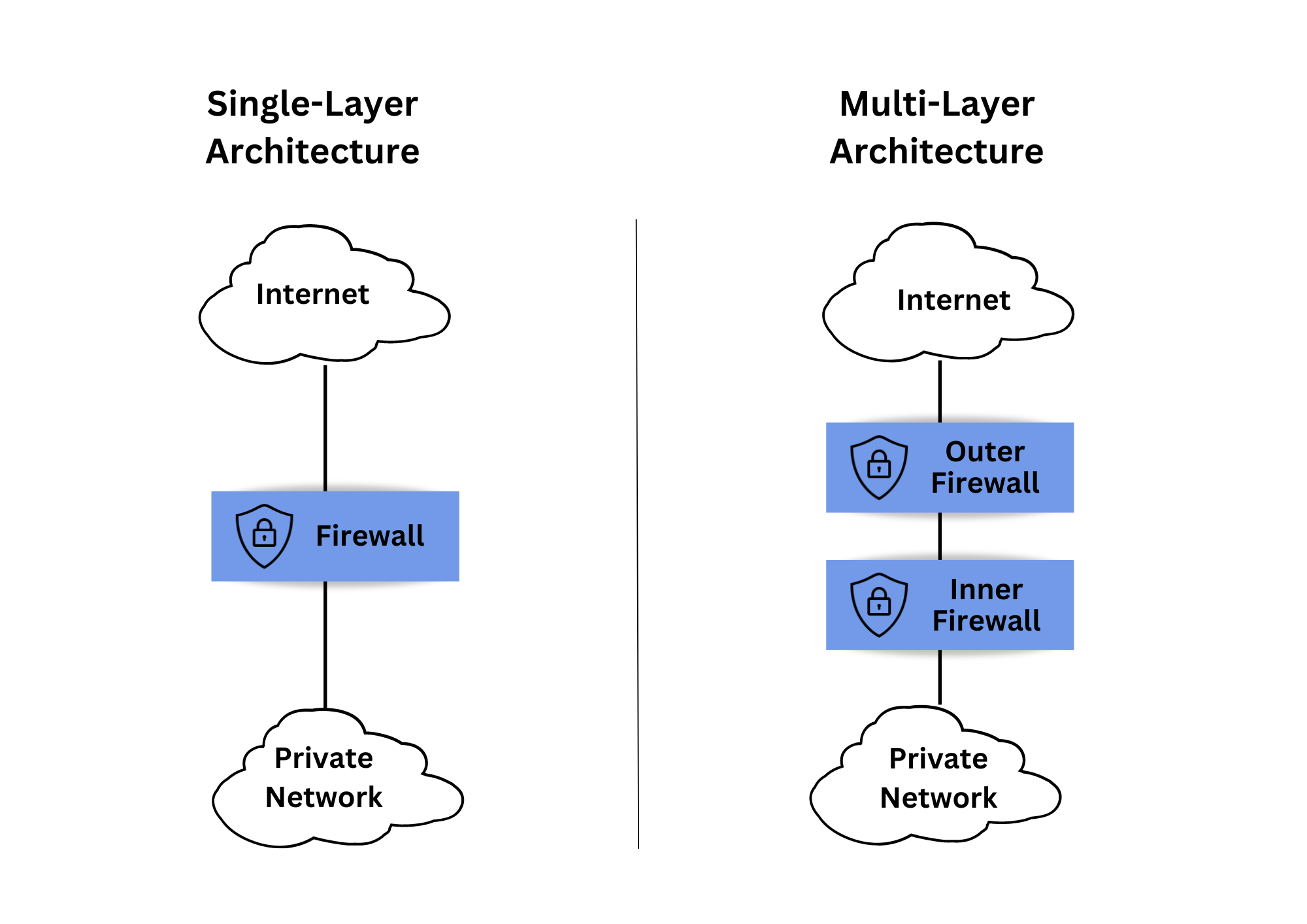
Single-Layer vs. Multi-Layer Architecture
With single-layer architecture, all the firewall functions are in a single network host. It’s a straightforward and cost-saving approach that’s applicable for a few interconnected networks. But it’s generally more prone to penetration in cases of misconfigurations or errors.
The firewall functions in multi-layer architecture are split between several network hosts that are commonly connected with demilitarized zone (DMZ) networks. This layered dual firewall approach is safer but costlier to implement and maintain and much harder to design.
Next, we finalize which functions will need to be implemented on the hosts. For example, this includes packet filtering, application proxies, and stateful inspection (also referred to as dynamic packet filter firewalls) to cover various services, from protecting IP addresses and HTTP to DNS. We also work on the security policies and decide on the needed network resources, authorization controls, and access policies.
Step 4: Defining the architecture characteristicsWhen designing a firewall system, it is important to determine how critical some firewall technology aspects are. For instance, this regards availability, performance, reliability, security, benefits vs. firewall pricing, ease of configuration, simplicity of management, maintenance complexity, and other characteristics.
Step 5: Creating system design documentationWe then put the firewall system design in the form of clear and detailed documentation with workflows and diagrams. It includes environment documentation, notes on the requirements, the appropriate firewall size, which vendor to choose, how to configure the firewall most optimally, how to enforce it, and so on.